DNSSEC is the extension of the DNS protocol that allows signing DNS data in order to secure the domain name resolving process. For general information about DNSSEC and its usage, visit ICANN website and IETF Tools.
Note: The support for DNSSEC is available in your hosting provider for Linux. The DNSSEC extension must be installed in your server by the hosting provider.
You can do the following to protect DNS data of your domains with DNSSEC:
- Sign and unsign domain zones according to DNSSEC specifications
- (Optionally) Specify custom settings to be used for generation of keys
- Receive notifications
- View and copy DS resource records
- View and copy DNSKEY resource record sets.
Signing a Domain Zone
To start using DNSSEC protection of your DNS zone, sign this zone. The hosting signs the zone with an automatically generated signatures using two pairs of asymmetric keys, the Key Signing Key (KSK) and the Zone Signing Key (ZSK).
To sign a domain zone:
- Select the domain in Websites & Domains.
- Go to DNSSEC and click Sign the DNS Zone.
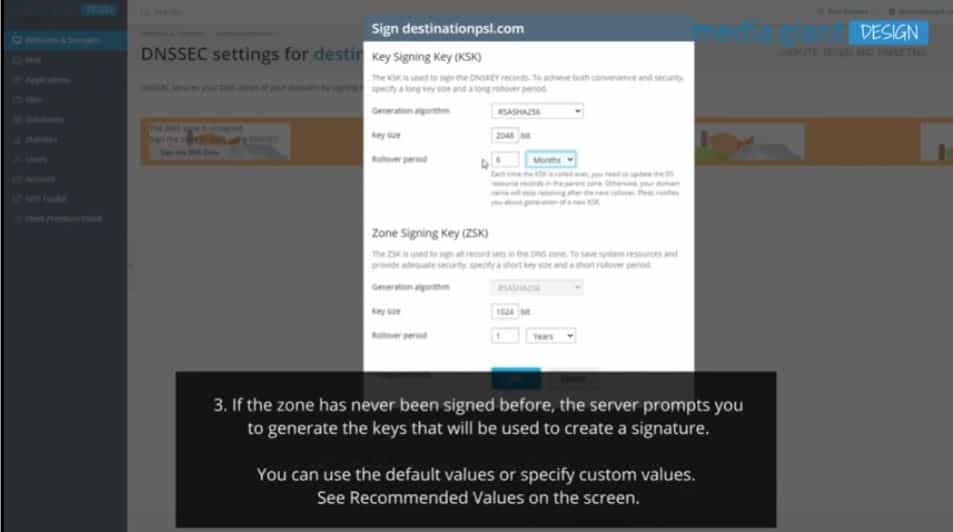
- If the zone has never been signed before, the server prompts you to generate the keys that will be used to create a signature.You can use the default values or specify custom values. See Recommended Values below.
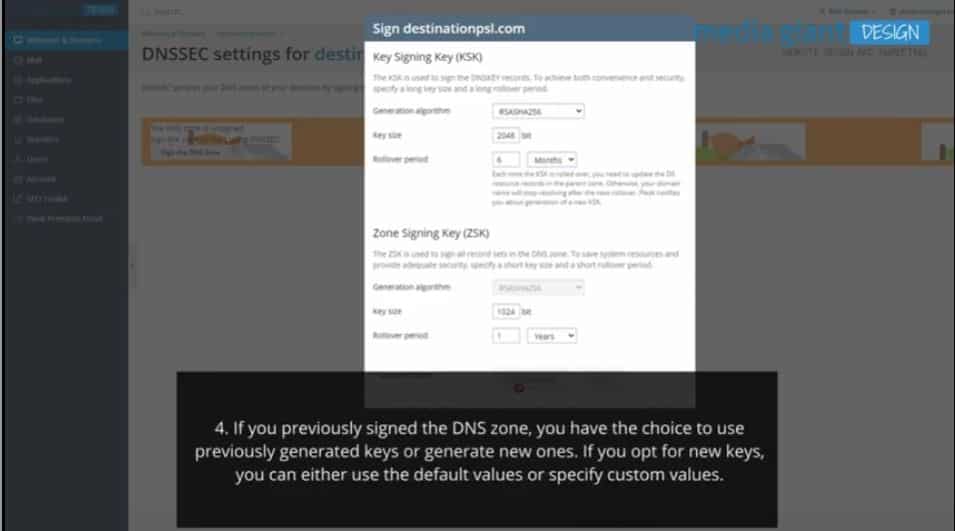
4. If you previously signed the DNS zone, you have the choice to use previously generated keys or generate new ones. If you opt for new keys, you can either use the default values or specify custom values. See Recommended Values below.
Recommended values of KSK and ZSK generation settings:
- A long key and a long rollover period for the KSK.Every time the Key Signing Key is updated, you need to update the DS records in the parent zone. The recommended values help you to update DS records as seldom as possible without decreasing security.
- A shorter key and a shorter rollover period for the ZSK.The Zone Signing Key is updated automatically. The recommended values help you to save system resources without decreasing security.
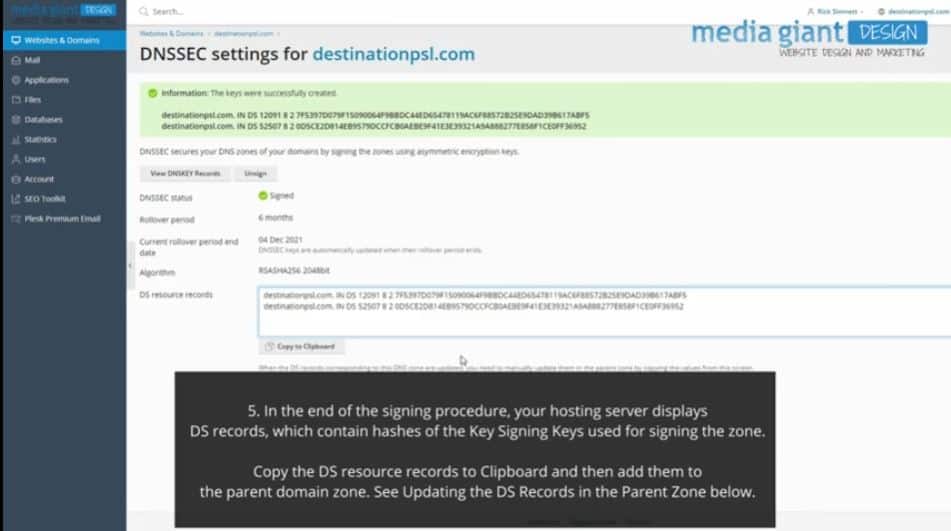
5. In the end of the signing procedure, your hosting server displays DS records, which contain hashes of the Key Signing Keys used for signing the zone.
Copy the DS resource records to Clipboard and then add them to the parent domain zone. See Updating the DS Records in the Parent Zone below.
Updating the DS Records in the Parent Zone
If the parent zone contains outdated DS records, the domain name is no longer resolved by the DNS service.
You will need to manually add or update DS records in the parent domain zone in all cases when DNSSEC keys were updated, namely:
- You signed a domain zone using newly generated keys.
- A KSK (Key Signing Key) rollover event took place.
Plesk sends you notifications and gives you some time to update the DS records – this period of time is equal to one KSK rollover period. During this period, the previous DS records are still valid.
If you unsigned the domain zone, you need to manually delete DS records in the parent domain zone.
To update DS records in the parent zone:
For a domain in your hosting server, whose parent zone is outside of the hosting server, update DS records at the domain’s registrar.
For a subdomain of a domain hosted in your server and having the DNS zone in your hosting:
- Go to DNS settings of the parent domain (Websites & Domains > go to the parent domain > DNS Settings).
- Add new records of the DS type (Add Record) and paste the values that display in the DS resource records box in the DNSSEC settings of the subdomain.
Unsigning a Domain Zone
Unsigning a domain zone turns off DNSSEC protection for that zone. You may need to unsign a zone if the keys were compromised, and then sign the zone again using new keys.
To unsign a domain zone:
- Go to Websites & Domains > select a domain > DNSSEC and click Unsign.
- Delete the DS resource records from the parent zone. Otherwise, the domain will not resolve.
Note: When you unsign a zone, the keys are not deleted from your hosting server. You can sign the zone again using the same keys.
Viewing DNSKEY Resource Records
You might need to retrieve DNSKEY resource records, which contain public parts of Key Signing Keys used by a domain.
To display DNSKEY records:
- Go to Websites & Domains > select a domain > DNSSEC.
- Click View DNSKEY Records.